Critical Report · May 2026
OT/ICS Security
Nigeria
Critical Infrastructure
May 2026
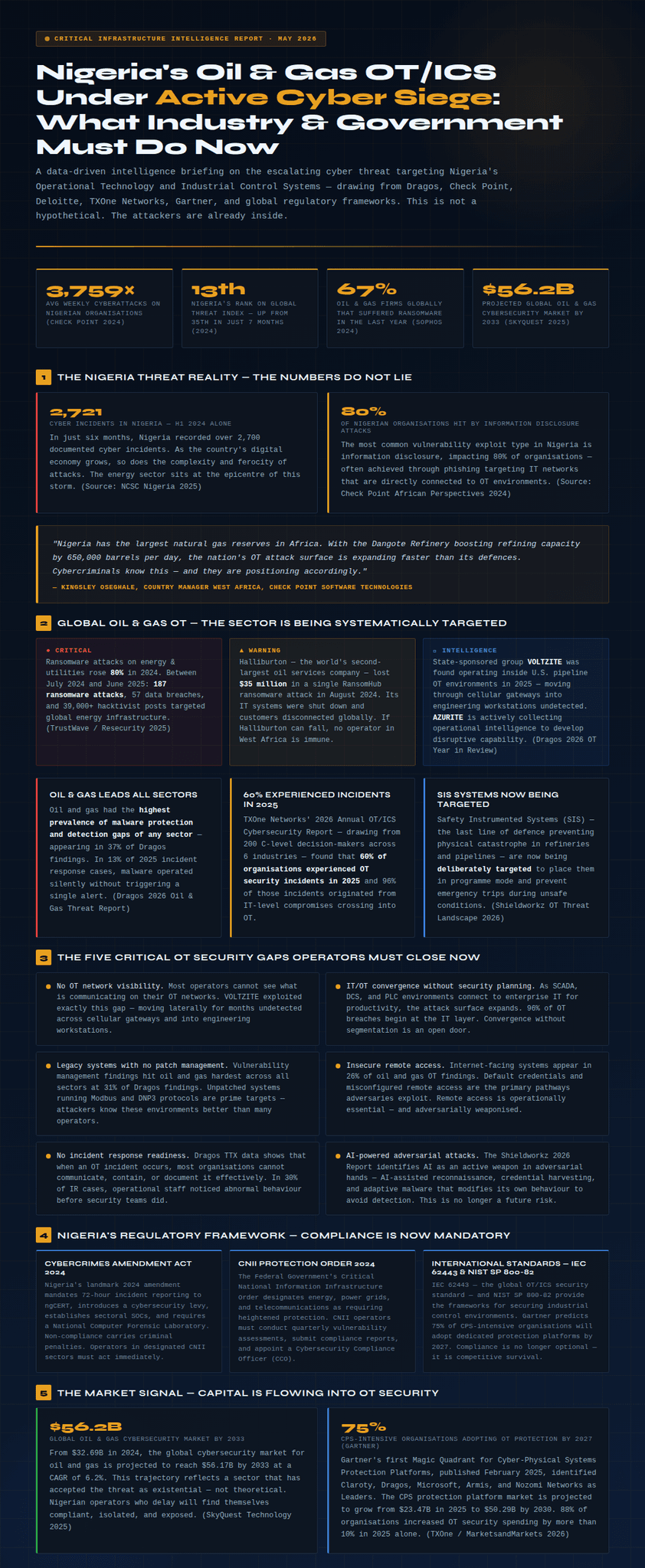
Nigeria's Oil & Gas OT/ICS Under Active Cyber Siege: What Industry & Government Must Do Now
A data-driven intelligence briefing on the escalating cyber threat targeting Nigeria's Operational Technology and Industrial Control Systems — drawing from Dragos, Check Point, Deloitte, TXOne Networks, Gartner, and global regulatory frameworks. The attackers are already inside.
3,759×Avg weekly cyberattacks on Nigerian orgs (Check Point 2024)
13thNigeria's rank on Global Threat Index — up from 35th in 7 months
67%Oil & gas firms globally hit by ransomware last year (Sophos 2024)
$56.2BProjected global oil & gas cybersecurity market by 2033
1The Nigeria Threat Reality — The Numbers Do Not Lie
2,721
Cyber incidents in Nigeria — H1 2024 alone
In just six months, Nigeria recorded over 2,700 documented cyber incidents. As the country's digital economy grows, so does the complexity and ferocity of attacks. The energy sector sits at the epicentre of this storm. (Source: NCSC Nigeria 2025)
80%
Of Nigerian organisations hit by information disclosure attacks
The most common vulnerability exploit type in Nigeria is information disclosure — most often achieved through phishing targeting IT networks directly connected to OT environments. Every connected SCADA system, every HMI panel, every PLC with a network interface is a potential entry point. (Source: Check Point African Perspectives 2024)
"Nigeria has the largest natural gas reserves in Africa. With the Dangote Refinery boosting refining capacity by 650,000 barrels per day, the nation's OT attack surface is expanding faster than its defences. Cybercriminals know this — and they are positioning accordingly."
— Kingsley Oseghale, Country Manager West Africa, Check Point Software Technologies
2Global Oil & Gas OT — The Sector Is Being Systematically Targeted
● Critical
Ransomware attacks on energy & utilities rose 80% in 2024. Between July 2024 and June 2025: 187 ransomware attacks, 57 data breaches, and 30,000+ hacktivist posts targeted global energy infrastructure. (TrustWave / Resecurity 2025)
▲ Warning
Halliburton — the world's second-largest oil services company — lost $35 million in a single RansomHub ransomware attack in August 2024. Its IT systems were shut down and customers disconnected globally. If Halliburton can fall, no operator in West Africa is immune.
◆ Intelligence
State-sponsored group VOLTZITE was found operating inside U.S. pipeline OT environments in 2025 — moving through cellular gateways into engineering workstations undetected. AZURITE is actively collecting operational intelligence to develop disruptive capability. (Dragos 2026 OT Year in Review)
60%
Organisations experienced OT security incidents in 2025
TXOne Networks' 2026 Annual OT/ICS Cybersecurity Report — drawing from 200 C-level decision-makers across 6 industries — found 60% of organisations experienced OT security incidents in 2025, with 96% of those incidents originating from IT-level compromises crossing into OT.
SIS
Safety Instrumented Systems now being deliberately targeted
SIS — the last line of defence preventing physical catastrophe in refineries and pipelines — are now being deliberately targeted to cause process upsets and prevent emergency trips during unsafe conditions. This represents a fundamental escalation in threat posture. (Shieldworkz OT Threat Landscape 2026)
Oil and gas has had the highest prevalence of malware protection and detection gaps of any sector — appearing in 37% of Dragos findings. In 13% of 2025 incident response cases, malware operated silently without triggering a single alert.
3The Five Critical OT Security Gaps Operators Must Close Now
⚠️No OT network visibility. Most operators cannot see what is communicating on their OT networks. VOLTZITE exploited exactly this gap — moving laterally for months undetected across cellular gateways into engineering workstations. You cannot protect what you cannot see.
⚠️IT/OT convergence without security planning. As SCADA, DCS, and PLC environments connect to enterprise IT for productivity gains, the attack surface expands dramatically. 96% of OT breaches begin at the IT layer. Convergence without deliberate segmentation is an open door to adversaries.
⚠️Legacy systems with no patch management. Vulnerability management findings hit oil and gas hardest across all sectors at 31% of Dragos findings. Unpatched systems running Modbus, DNP3, and proprietary industrial protocols are prime targets — attackers understand these environments often better than the operators themselves.
⚠️Insecure remote access. Internet-facing OT systems appear in 26% of oil and gas findings. Default credentials and misconfigured remote access are the primary pathways adversaries exploit. Remote access is operationally essential — and adversarially weaponised.
⚠️No OT-specific incident response readiness. In 30% of IR cases, operational staff noticed abnormal behaviour before security teams did — a fundamental detection gap. AI-assisted reconnaissance, credential harvesting, and adaptive malware are now current operational reality. (Shieldworkz 2026)
4Nigeria's Regulatory Framework — Compliance Is Now Mandatory
Cybercrimes Amendment Act 2024
Nigeria's landmark 2024 amendment mandates 72-hour incident reporting to ngCERT, introduces a cybersecurity levy, establishes sectoral SOCs, and requires a National Computer Forensic Laboratory. Non-compliance carries criminal penalties including fines and imprisonment.
CNII Protection Order 2024
The Federal Government's CNII Order designates energy, power grids, and telecommunications as requiring heightened protection. CNII operators must now:
Conduct quarterly vulnerability assessmentsSubmit compliance reports to the National Cybercrime CentreAppoint a dedicated Cybersecurity Compliance Officer (CCO)
IEC 62443 & NIST SP 800-82
The global OT/ICS security standards providing the proven frameworks for securing industrial control environments. Gartner predicts 75% of CPS-intensive organisations will adopt dedicated OT protection platforms by 2027. Compliance is no longer optional — it is competitive survival.
5The Market Signal — Capital Is Flowing Into OT Security
$56.2B
Global oil & gas cybersecurity market by 2033
From $32.69B in 2024, the global cybersecurity market for oil and gas is projected to reach $56.17B by 2033 at a CAGR of 6.2%. This trajectory reflects a sector that has accepted the threat as existential — not theoretical. (SkyQuest Technology 2025)
75%
CPS-intensive organisations adopting OT protection by 2027 (Gartner)
Gartner's first Magic Quadrant for Cyber-Physical Systems Protection Platforms (February 2025) confirms that the world's largest industrial operators are investing now. 88% of organisations increased OT security spending by more than 10% in 2025 alone. (TXOne Networks / Frost & Sullivan 2026)
Nigerian oil and gas operators who delay will find themselves isolated, non-compliant, and exposed — while global peers build OT resilience frameworks that protect production, people, and national revenue.
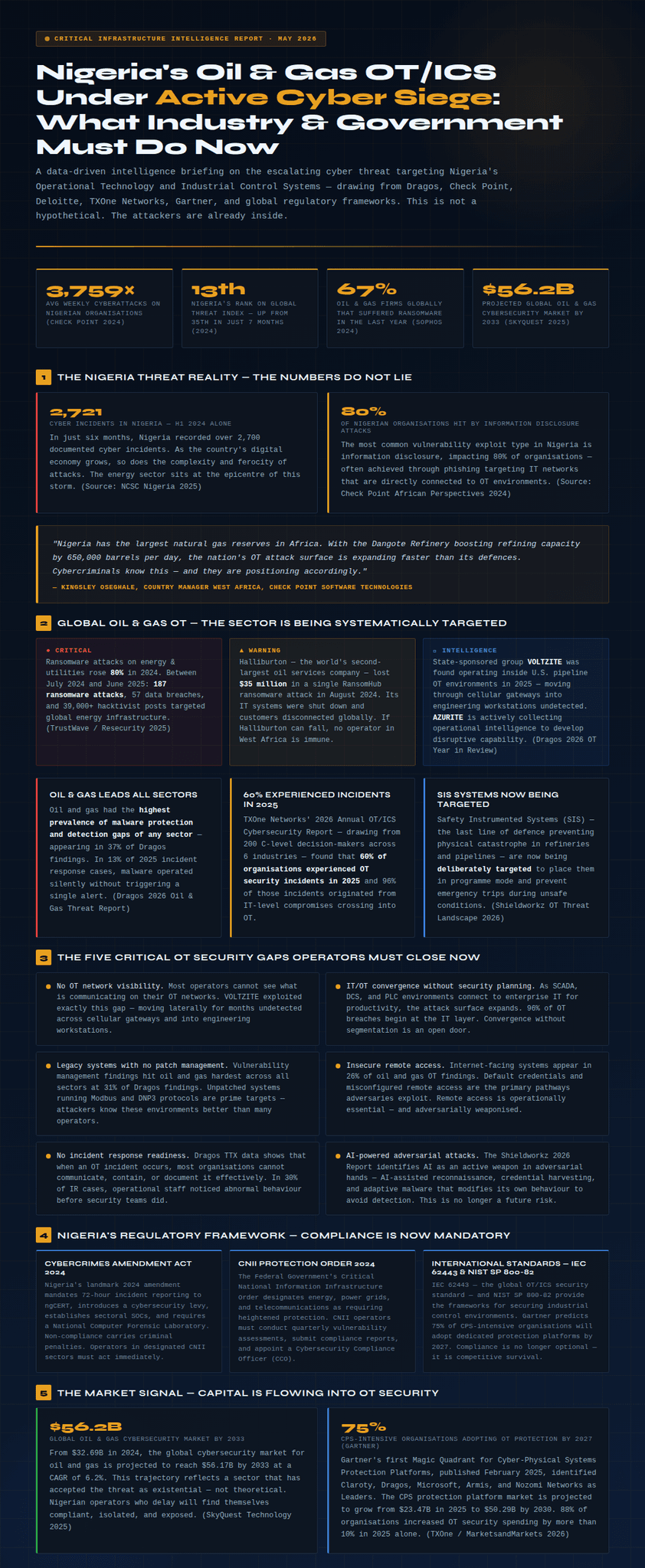
6The Call to Action — For Industry and Government
The threat is real. The regulations are in place. The global market is responding decisively. Nigeria's oil and gas sector — the backbone of the nation's economy — must match that urgency.
Immediate Action Required
For Operators & Industry Decision-Makers
Commission an OT/ICS risk assessment aligned with IEC 62443
Deploy continuous OT network monitoring and asset visibility
Segment IT and OT networks with a deliberate Zero Trust architecture
Establish and test an OT-specific incident response plan
Ensure all remote access points are authenticated, encrypted, and monitored
For Government & Regulatory Agencies (NNPC, DPR, NERC, ngCERT, NITDA)
Mandate OT cybersecurity assessments for all licensed operators
Enforce CNII compliance across energy and petroleum infrastructure
Fund national OT cybersecurity capacity building and skills development
Establish a dedicated OT-CERT for the Nigerian energy sector
Create public-private partnerships with global OT security specialists
"The cost of a cyber breach will almost always exceed the cost of investing in effective cybersecurity measures and tools. The question Nigerian operators must answer is not whether they can afford OT security — it is whether they can afford to be the next Halliburton."
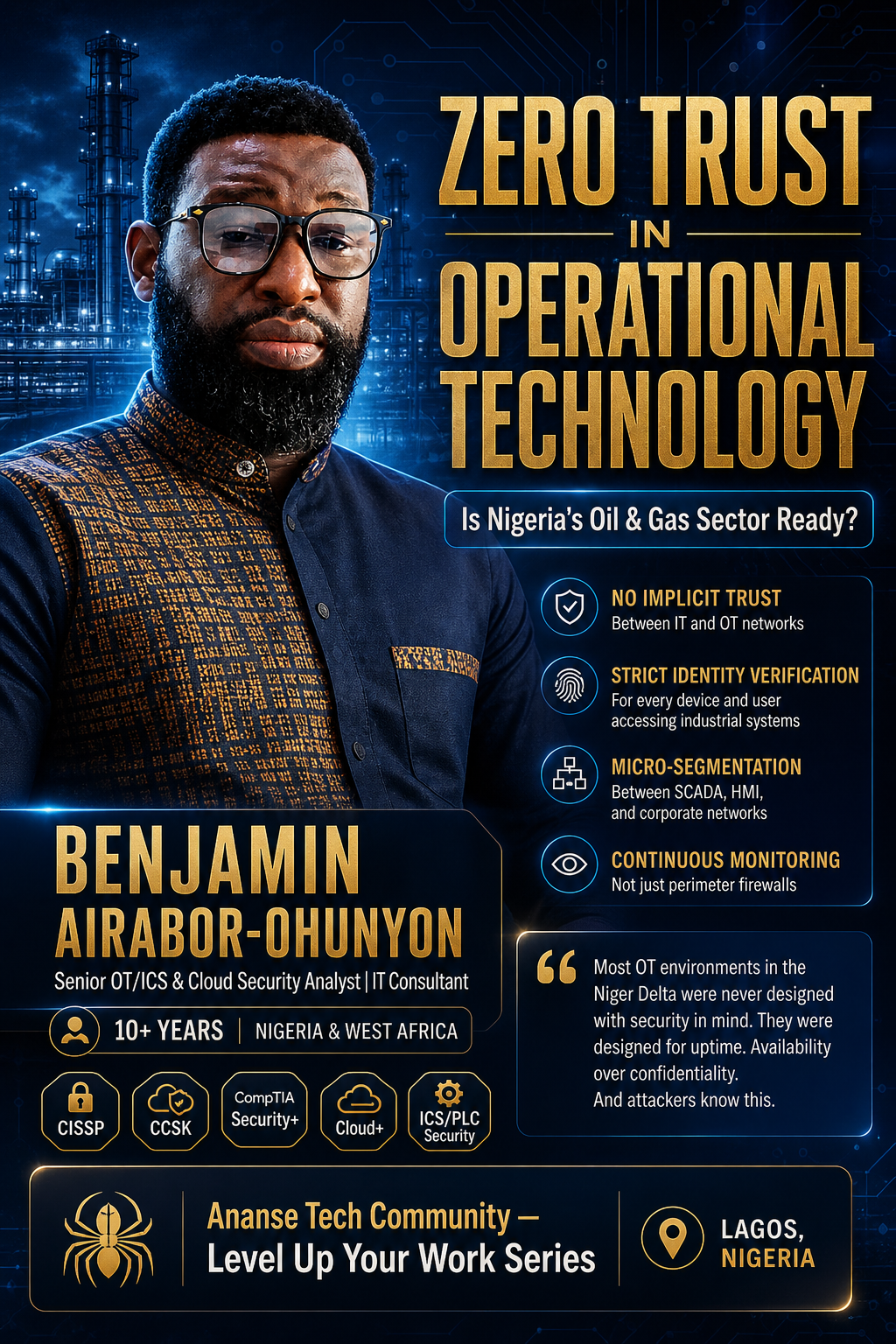
— Benjamin Airabor-Ohunyon · Airabor-Ohunyon Business Ventures · May 2026
● Critical — Nigeria Threat Reality
2,721 Cyber Incidents in H1 2024 Alone
Nigeria moved from 35th to 13th on the Global Threat Index in just seven months. Ransomware on energy & utilities rose 80% in 2024, with 57 data breaches targeting global energy infrastructure. The most common exploit: information disclosure impacting 80% of Nigerian organisations, typically via phishing into IT networks directly connected to OT.
▲ Warning — Global Oil & Gas OT
60% of Organisations Experienced OT Incidents in 2025
TXOne Networks 2026 found 60% of organisations experienced OT incidents in 2025, with 96% originating from IT compromises crossing into OT. Halliburton lost $35 million in a single ransomware attack in August 2024. SIS systems are now being deliberately targeted to cause physical harm.
The 5 Critical OT Security Gaps Nigerian Operators Must Close Now
⚠️No OT network visibility. VOLTZITE moved laterally for months undetected. You cannot protect what you cannot see.
⚠️IT/OT convergence without security planning. 96% of OT breaches begin at the IT layer. Convergence without segmentation is an open door.
⚠️Legacy systems with no patch management. Unpatched Modbus and DNP3 systems are prime targets — attackers often know these environments better than operators.
⚠️Insecure remote access. Internet-facing OT systems appear in 26% of oil & gas findings. Default credentials are the primary pathway adversaries exploit.
⚠️No OT-specific incident response readiness. In 30% of IR cases, operational staff noticed abnormal behaviour before security teams did. AI-powered attacks are now current operational reality.
Regulatory Framework — Compliance Is Now Mandatory
Cybercrimes Amendment Act 2024
Mandates 72-hour incident reporting to ngCERT, introduces a cybersecurity levy, establishes sectoral SOCs. Non-compliance carries criminal penalties.
CNII Protection Order 2024
CNII operators must conduct quarterly vulnerability assessments, submit compliance reports, and appoint a dedicated Cybersecurity Compliance Officer (CCO).
IEC 62443 & NIST SP 800-82
Gartner predicts 75% of CPS-intensive organisations will adopt dedicated OT protection platforms by 2027. Compliance is competitive survival.
The Market Signal — Capital Is Flowing Into OT Security
$56.2B
Global oil & gas cybersecurity market by 2033 (CAGR 6.2%). Nigerian operators who delay will be isolated, non-compliant, and exposed.
OT security spending ↑10%+ in 202588%
Orgs deploying OT protection by 202775%
Oil & gas OT incidents in 202560%
Orgs hit by info disclosure (Nigeria)80%
"The cost of a cyber breach will almost always exceed the cost of investing in effective cybersecurity measures and tools. The question Nigerian operators must answer is not whether they can afford OT security — it is whether they can afford to be the next Halliburton."
— Benjamin Airabor-Ohunyon · Airabor-Ohunyon Business Ventures · May 2026